Subtotal $0.00
Shopping cart
Recent Posts
Subscribe
Sign up to get update news about us. Don't be hasitate your email is safe.
Sign up to get update news about us. Don't be hasitate your email is safe.

 Fact Checked by Coinsbeat Editorial Team | Expert Reviewed by Themiya
Fact Checked by Coinsbeat Editorial Team | Expert Reviewed by ThemiyaThe wallet gets drained, the post-mortems go up, Twitter loses its mind for 48 hours, and then the market moves on. That’s the story most people tell themselves about a crypto exploit. It’s also completely wrong.
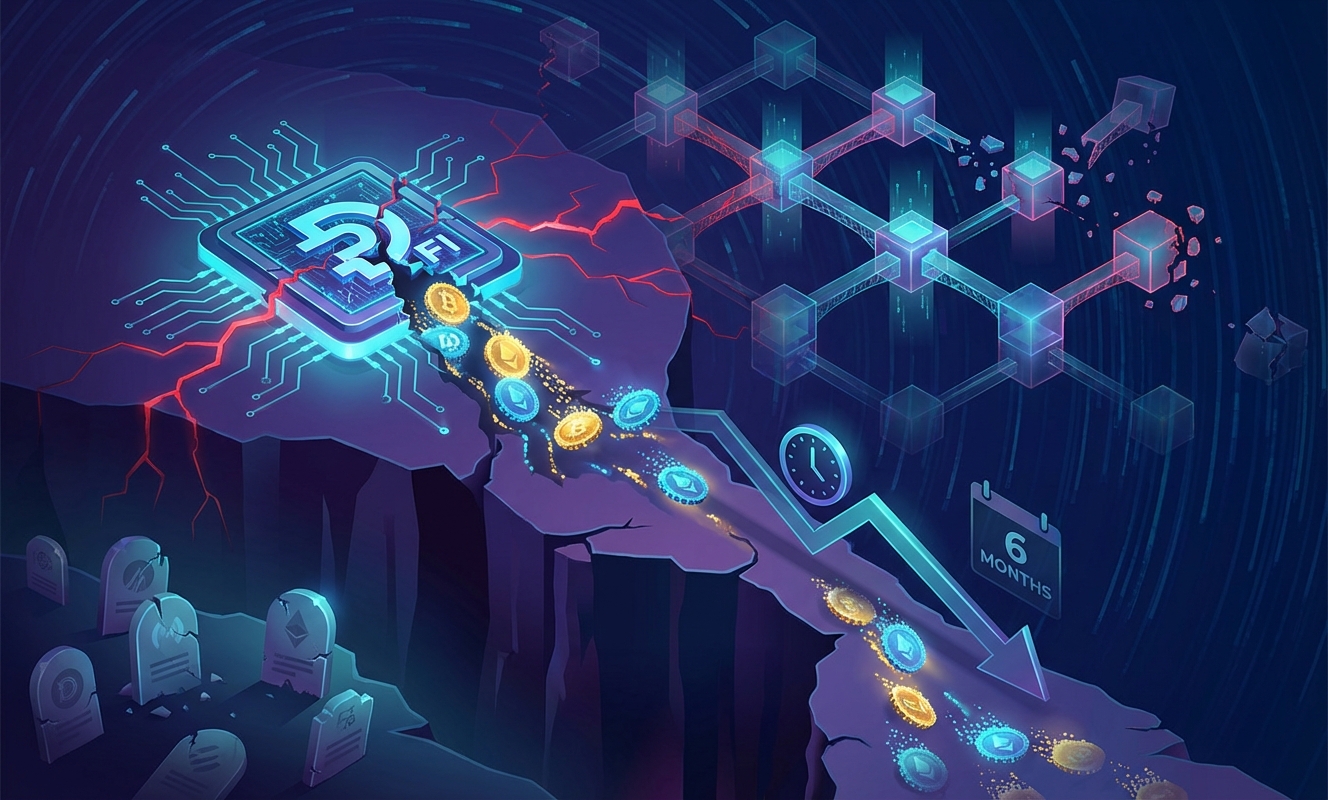
Immunefi just dropped its “State of Onchain Security 2026” report, and the number that should be keeping every DeFi founder up at night isn’t the $4.67 billion stolen across 2024 and 2025. It’s this: 84% of hacked tokens never recovered to their pre-hack price within six months. Median decline over that window? 61%. Let that sink in.
The theft is the trigger. The slow bleed is the actual kill shot.
Immunefi tracked 191 hacks across 2024 and 2025. The raw headline number, $4.67 billion, sounds catastrophic. And it is. But the way that number is structured tells you something far more disturbing about where the risk actually lives.
The median hack was $2.2 million. Down from $4.5 million in the 2021-2023 cycle. On the surface, that looks like the industry got smarter. It didn’t. Look closer.
Here’s the thing about a distribution like this. It creates a false sense of security at the median level. Most projects look at the average hack size and think, “We can survive a $2 million exploit.” Maybe. But the tail risk? That’s where a single catastrophic event rewrites the entire year’s narrative in one afternoon.
The number of hacks per year barely moved. 94 in 2024, 97 in 2025, almost identical to 2023. The industry has essentially normalized this. Hacks are no longer a crisis to be solved. They’re a recurring line item.
Let’s be real about something the decentralization crowd tends to gloss over. Of the 191 hacks in Immunefi’s dataset, only 20 involved centralized exchanges. Twenty. That’s roughly 10% of all incidents.
Those 20 incidents produced $2.55 billion in losses, or 54.6% of all stolen funds.
Think about that ratio for a second. A tiny fraction of attack vectors is responsible for the majority of actual damage. The problem isn’t just buggy smart contracts or poorly audited DeFi protocols. It’s the places where trust, custody, and key management get concentrated into a single point of failure. Bybit proved this at scale.
Honestly, this is the part of the report that deserves more attention than it’s getting. The DeFi community loves to point at centralized venues as dinosaurs. But if CEXes are generating over half the losses from a tenth of the attacks, the conversation about systemic risk needs to start there, not with some obscure bridge protocol nobody’s heard of.
This is the section of Immunefi’s report that I think most analysts are underweighting. The price damage data.
Immunefi analyzed 82 hacked tokens. The immediate shock, the two-day median decline, was roughly 10%. Bad, but survivable. Then look at what happens next.
Why does this happen? Because in crypto, the token isn’t just a speculative asset. It’s the treasury. It’s the recruitment tool. It’s the partnership leverage. It’s the public sentiment barometer that counterparties and investors check before every deal. When it craters and stays down, everything downstream craters with it.
Teams lose security leadership within weeks. Three months get consumed by recovery work instead of shipping product. Partners who were in diligence quietly walk away. The company that was supposed to build something is now spending its energy fighting for basic credibility.
And this plays out in a market environment where information moves faster than any PR team can respond. Counterparties reprice their exposure before the internal cleanup is even finished. That’s a brutal structural disadvantage that most projects simply aren’t capitalized enough to survive.
Look, DeFi composability is genuinely impressive. Bridges, liquid staking, restaking, lending markets, stablecoins all snapping together like financial Lego. The innovation is real. So is the fragility it creates.
Immunefi’s argument is that this interconnectedness creates longer vulnerability chains. A compromise doesn’t stay contained to the protocol where it originated. It travels. It hits dependent protocols. It drains liquidity from adjacent markets. It triggers collateral cascades.
This isn’t hypothetical. We’ve seen it. Every major DeFi exploit of the last three years has had second and third-order effects that weren’t visible until the dust settled. The more integrated the ecosystem becomes, the farther a single exploit can travel before anything stops it.
To be fair, Immunefi acknowledges it can’t always cleanly separate hack damage from pre-existing project weakness or broader market conditions. Some of these tokens were fragile long before anyone touched the code. Illiquid, overvalued, losing momentum. The hack was the match, but the kindling was already there.
Still. The pattern is hard to dismiss.

From a cold-blooded portfolio perspective, here’s what this data actually means for anyone allocating capital in this space.
Here’s the real danger the report surfaces for anyone holding tokens in protocols that haven’t been tested yet. The projects most likely to get wiped out post-hack aren’t necessarily the ones with the worst code. They’re the ones that were already undercapitalized, already losing narrative momentum, and already operating with thin liquidity in their token markets.
A hack doesn’t create fragility. It reveals it.
If you’re holding a governance token in a protocol with low TVL, thin trading volume, and a small treasury relative to its market cap, you are already sitting on a recovery-impossible situation if anything goes wrong. The hack is just the event that makes it visible to everyone else.
The industry has 425 hacks and $11.9 billion in losses over five years to learn from. The market hasn’t gotten meaningfully safer. It’s just gotten better at absorbing the shock and moving on. Whether that’s resilience or denial probably depends on which side of the next exploit you end up on.
References & Sources:
The 30-day rule in crypto, often compared to the “wash sale rule” in traditional finance, dictates how the cost basis of an asset is calculated for tax purposes. If a trader sells a cryptocurrency at a loss and repurchases the exact same type of token within a 30-day window, they may be restricted from claiming that initial loss on their taxes. While the strict application of this rule currently varies by jurisdiction, it is crucial for crypto investors to understand it to avoid unexpected tax liabilities—especially when hastily liquidating assets after market downturns or recovering from security breaches.
Crypto hacks don’t stop when the market crashes or liquidity dries up because cybercriminals are playing a long-term game. Even if the immediate fiat value of a token drops, the underlying infrastructure—like smart contracts and cross-chain bridges—retains the same code vulnerabilities. Hackers exploit these weaknesses to hoard massive volumes of tokens while they are cheap, storing them in decentralized cold wallets. They then wait patiently for the next bull run to cash out at a massive profit. Furthermore, state-sponsored hacking groups steal crypto primarily to bypass international financial sanctions, making the current dollar value secondary to the borderless utility of the asset.
Once a protocol is hacked and the money is seemingly “gone,” cybercriminals employ sophisticated laundering techniques to permanently obscure the digital paper trail. They frequently deploy decentralized coin mixers (such as Tornado Cash) that pool and scramble stolen funds with legitimate transactions, breaking the blockchain’s deterministic link. Hackers also heavily rely on “chain-hopping”—rapidly swapping tokens across multiple different blockchains using unregulated decentralized exchanges (DEXs) and cross-chain bridges. Finally, they often convert the stolen assets into privacy coins like Monero or funnel them through rogue, non-compliant exchanges to safely extract fiat currency.
Recovering stolen cryptocurrency is extremely challenging due to the immutable nature of blockchain technology, meaning transactions cannot simply be reversed by a central authority. However, recovery is not completely impossible. Cybersecurity firms and blockchain sleuths actively monitor the movement of stolen funds. If a hacker attempts to cash out through a centralized exchange with strict KYC (Know Your Customer) protocols, law enforcement can step in to freeze the wallets. In many modern DeFi exploits, protocols actually negotiate directly with the attacker, offering them a multi-million dollar “white-hat bounty” to legally keep a portion of the funds in exchange for safely returning the rest.
Expert in Digital Marketing and Cryptocurrency News with a BSc (Hons) in Marketing Management. With over 06 Years of experience in the blockchain space, Themiya provides in-depth analysis and technical insights for Coinsbeat.